Automated Pentesting with Trython
With Automated Pentesting, simulate real-world attack paths at machine speed using AI-driven techniques. Our Automated Pentesting engine replicates how attackers probe networks, applications, and endpoints, producing high-fidelity, actionable reports.
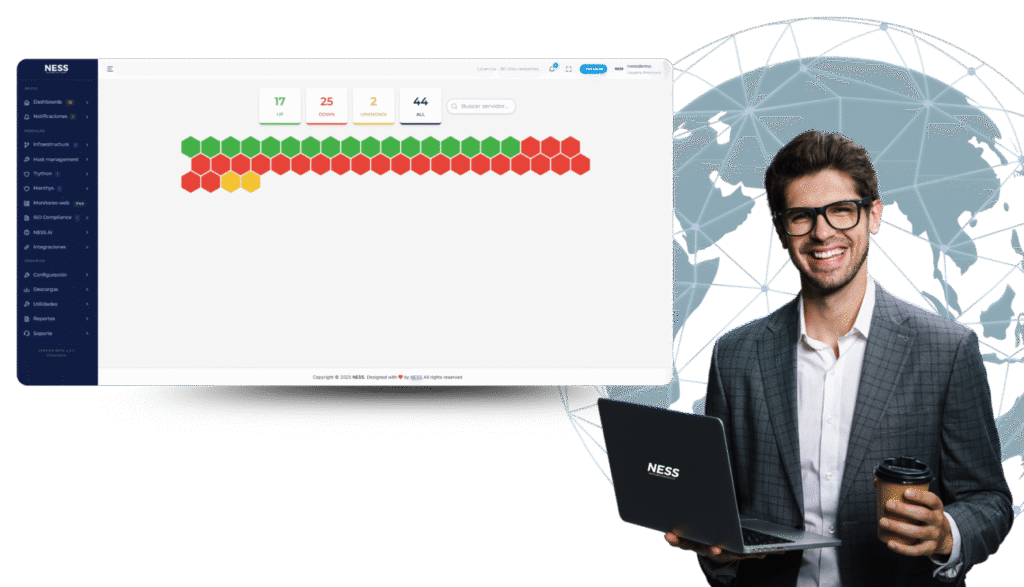
Automated pentesting
in NESS
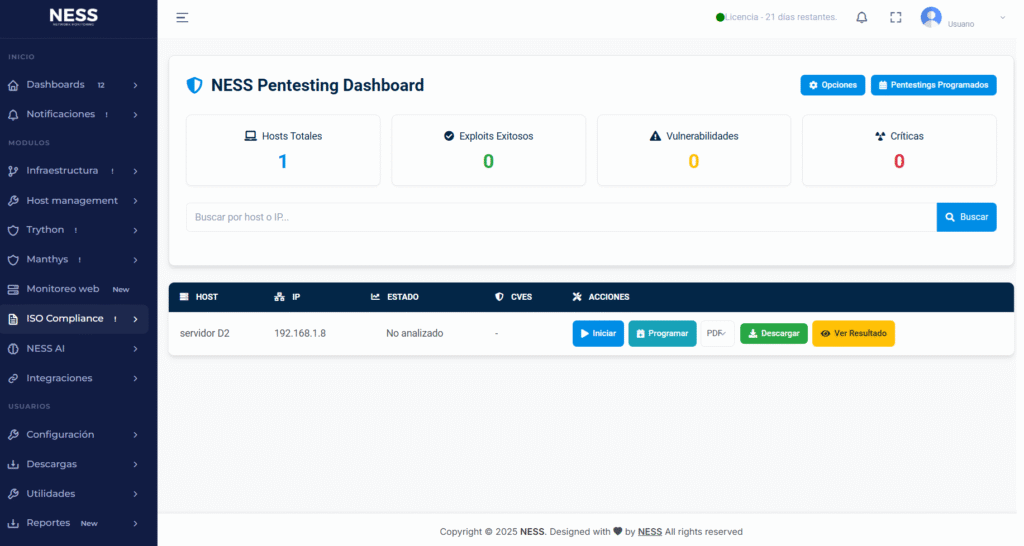
With Automated Pentesting, you get more than a list of vulnerabilities — you get a complete, visual inventory of exploitable weaknesses in your environment. Each finding in our Automated Pentesting reports includes its level of criticality, likelihood of exploitation, and potential business impact.
For every test, Automated Pentesting provides reproducible technical evidence such as execution logs, network traces, session captures, proof-of-concept (PoC) examples, and detailed output that clearly demonstrate each attack vector.
You also gain access to interactive dashboards with key metrics — exploitable vulnerabilities, average remediation time, severity trends, and risk-reduction percentage — updated after every Automated Pentesting run.
We don’t just identify problems; Automated Pentesting delivers concrete, prioritized action plans including patches, configuration adjustments, firewall rules, segmentation, and service hardening. Each recommendation includes estimated effort and expected impact to help your team make efficient, informed decisions.
Automated pentesting: real attacks and results
NESS Automated Pentesting simulates real cyberattacks to identify vulnerabilities before hackers can exploit them. With our advanced Automated Pentesting technology and clear, actionable reports, you gain the insights needed to strengthen your security posture and protect your company’s most critical assets — all without disrupting your daily operations.
The automated pentesting process
Our Automated Pentesting process combines advanced technology with professional methodology to detect, assess, and remediate vulnerabilities quickly and accurately.
From scope definition to final validation, every Automated Pentesting phase is designed to strengthen your infrastructure, reduce risks, and ensure your critical assets remain protected against real-world cyberattacks.
NESS automated pentesting replicates tactics, techniques, and procedures
With Automated Pentesting, you can run security tests on demand or schedule them as part of a continuous assessment strategy. Thanks to automation, results are displayed in a centralized dashboard with real-time alerts and detailed reports, giving you complete visibility and control over your organization’s security posture.

NESS (Network Environment Scanning and Security), focuses on developing software to help companies prevent and predict cyberattacks and failures within their technological infrastructure.